Custom Tunnelblick/OpenVPN Configuration Settings for proXPN
Posted: December 14, 2014 Filed under: Internet, OS X, Security | Tags: Apple, Configuration, Internet, Macintosh, OS X, Security, Software, VPN 1 CommentDownload proXPN Tunnelblick Configuration
After hearing proXPN marketed by Steve and Leo on the TWIT “Security Now” (SN) podcast for several months I decided to sign up for the service and take advantage of the SN promotional 50-percent off discount. By the way, if you have not been listening to the Security Now podcast or if you have never heard of it I encourage you to check it out. I had trouble connecting to the proXPN servers using the provided client software on Macintosh OS X 10.9.5 (other versions of OS or client were not tested) so I created a set of configuration files so that I could use an unbranded version of Tunnelblick.
When I realized that the proXPN OpenVPN client software was simply a rebranded version of the popular OS X OpenVPN client Tunnelblick I used the Tunnelblick instructions for removing rebranded versions of Tunnelblick. I then installed the standard Tunnelblick and attempted to configure it using Mark Lai’s instructions for using proXPN with Tunnelblick. After doing a few basic tests I confirmed that I could use proXPN’s service on my Macintosh running OS X 10.9.5 and Tunnelblick.
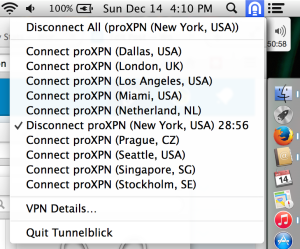
I wanted to keep all, or at least most, of the options/features offered by the proXPN client but using the standard non-branded Tunnelblick. By evaluating the OpenVPN documentation and the logs produced by OpenVPN packaged with Tunnelblick I decided to make a few modifications to the OpenVPN configuration files and to develop a set of configuration files so that I could utilize the various ports, servers and locations offered by the proXPN service. These configuration files utilize several security options documented by OpenVPN and do not utilize any up/down scripts supplied by proXPN. You may download and submit bugs/features against these configuration files at my github page. Installation instructions are provided there as well. These configuration files include the primary and secondary addresses off all the locations and will attempt to connect on ports 1194, 443, 80 and 8080 in that order. See screenshot above for what Tunnelblick looks like after these configuration files are installed.
I would also like to point out that I tried a competing paid ($9 USD) OpenVPN client for OS X titled “Viscosity.” Viscosity does not appear to be updated as often as Tunnelblick. For a security application this is a bit of a concern to me. Viscosity is not open source like Tunnelblick. Viscosity has a few bugs at the moment that prevented me from being able to use or test the product. These bugs prevent a user from importing existing OpenVPN configuration files. When I attempted to manually create and modify configurations from within Viscosity I was not able to connect. After getting Tunnelblick to work and spending some time on Viscosity I lost interest and patients. I have some UI complaints against Tunnelblick but they are mostly the same with Viscosity so I really was not that motivated to get Viscosity to work.
As a whole I feel pretty disappointed in the state and availability of OpenVPN clients for OS X but I’m happy I found a solution that appears to work well for me. I have decided to stay with paid/premium proXPN service for the next year instead of bailing out during the 7-day grace period. Hopefully the proXPN quality of service will overcome my OpenVPN client issues. I still have clients to configure for iOS 8, Arch Linux and Windows 7. By the time I am done configuring all of these clients, I expect to have a decent impression of how OpenVPN clients are implemented across various popular operating systems.
Download proXPN Tunnelblick Configuration
Hacking Apple Headphones for Assistive Technology
Posted: December 7, 2013 Filed under: Hardware | Tags: Apple, Assistive Technology 1 Comment A while back I took opportunity to hack together a piece of Assistive Technology (AT) for a good friend of mine using a damaged pair of Apple Earphones with Remote and Mic. The first version, pictured on the right, is constructed with a three button array found on ebay.
A while back I took opportunity to hack together a piece of Assistive Technology (AT) for a good friend of mine using a damaged pair of Apple Earphones with Remote and Mic. The first version, pictured on the right, is constructed with a three button array found on ebay.
The second version, pictured at the bottom, is constructed with large arcade buttons from Sparkfun and a custom enclosure that I made with sheet metal, a breaker bar and pop (blind) rivets. This version should be easier to use than the first as it has larger softer buttons, less dangling wires and a case that can withstand being squished between an electric wheel chair and a door frame.
If you are interested in what is inside the Apple Earphone controller, there is a wonderful tear down post.